
Neither external cybersecurity training programs nor current on-the-job methods are getting it done.
Solar Winds. Keseya. Colonial Pipeline. Microsoft Exchange. JBS.
Every month, it seems like another company is in the news for a cyber breach, as hackers and cyber gangs appear to have gained an upper hand in the battle to exploit digital information, networks, and businesses. Looking at a report published by ISC2 back in 2019, however, this is a predictable outcome, based on the global shortage of cybersecurity talent. At the time, ISC2 estimated there were over 4M cybersecurity jobs that were unfilled or underfilled (staffed by someone without the requisite skills to do the job).
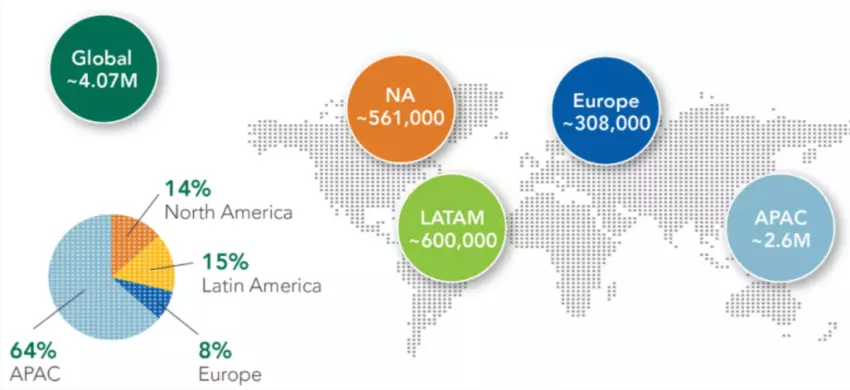
Image: Global shortage of cybersecurity talent by region.
Since 2019, that gap has only grown larger while attackers have grown more sophisticated. It’s no wonder that breaches seem to be on the rise.
On-the-job cybersecurity training has always been an important component of taking someone with raw knowledge and transforming them into effective analysts. But with cybersecurity being a relatively new and dynamic skill, traditional pipelines for producing professional workers, such as academia, have failed to keep pace. Additionally, the field changes so rapidly that by the time a student graduates from a program and starts a job, they need more than just on-the-job training. They need to update their knowledge base to reflect the latest trends, exploits, threat groups, and attack vectors.
This is a situation that most large companies are struggling with: how to recruit, train, evaluate, and retain qualified cybersecurity talent in order to ensure the security operation center is effective at stopping malicious activity.
What the Best Cybersecurity Training Programs Entail
A consistent cybersecurity training program and evaluation of fraud analysts against a relevant, up-to-date standard is a critical component of that cycle. That means:
Choosing a standard that is fundamental enough to remain relevant through changes in the threat landscape, technology ecosystem, and organizational changes
Consistently updating training scenarios to include the latest exploits used by attackers
Ensuring that training takes place in the most realistic environment possible, with the tools and conditions where analysts actually do their job
The last point is especially important, and especially difficult for most companies to implement.
Several training programs meet the second criteria but require already short-staffed teams to send personnel away for days or weeks to external courses, where they study the latest exploits and learn about the latest cybersecurity technology. They may take an exam and leave with a certificate. When they return to their desk, however, they may or may not be any better at their actual job.
Conversely, standard on-the-job training, while more directly relevant to the “real work,” often lacks the structure of external courses. There’s typically no curriculum and no way to evaluate performance against a standard. Instead, supervisors judge individual performance based on checklists and discussion. Even with those subjective assessments, there’s little they can do to assign targeted, experiential training to help personnel obtain and demonstrate required levels of proficiency.
The ability to conduct in-production cybersecurity training and evaluation to a standard brings several advantages over the two primary training methods available today: external training and on-the-job training. Those advantages include:
A consistent framework for evaluation and training, with content that reflects the latest exploits and threat actors
A clear picture of current skill and readiness levels of individual analysts and the SOC as a whole
“Train where you fight,” using the exact same tools you use every day, on production
Continuous training and evaluation, as part of a daily, weekly, and monthly rhythm, without sending key personnel away for days or weeks so we can know they are ready to perform
Training Your Analysts to the Highest Standards
SightGain has spent years working with the top cybersecurity teams in the Department of Defense to help train their analysts to the highest standards. Now this technology is available to commercial Security Operations Center (SOC) managers as well.
SightGain gives SOC managers the ability to train their team on their production environment with the tools they use every day to do their job and evaluate their performance against a nationally recognized standard, like the NICE Framework. They can use SightGain to run their own internal “cyber academy” tailored to their specific tools, their environment, and their Standard Operating Procedures. This training also uses the latest and most relevant threat-based exploits, which are updated as the threat landscape evolves.
By leveraging this innovative capability and approach, we hope to help more companies with their most valuable asset in the cybersecurity battle: their people.
To find out more and book a product demo, visit www.sightgain.com.

